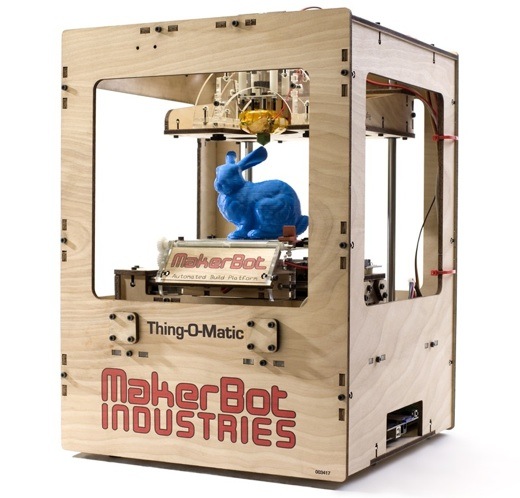
 Image above: A plastic rabbit out of a 3D printing tophat called Thing-O-Matic. From (http://www.digitaltrends.com/computing/what-is-3d-printing-a-beginners-guide-to-the-desktop-factory/).
This piece below by Jeremy Rifkin struck me as an exercise in delusional thinking used for mass deception. When Rifkin mentions that "mobile phones, auto and aircraft parts, medical implants, and batteries are being 'printed out' with 3D printers he is talking about industrial design components created by professionals as prototypes - not finished manufactured items.
With the introduction of 3D Systems' first commercial 3D printers, about 20 years ago, the industrial design of mass produced products has been revolutionized - especially complex 3D entities like auto taillight assemblies. But once the design is settled the actual production is still done using plastic injection molding technology.
The idea that your average Joe will design and "print-out" something even as simple as a usable/durable ratchet-set or Vise-grip made out of plastic from a consumer 3D printer hooked up to a laptop is ridiculous. The stresses on these "printed" plastic products would be too great for practical application, moreover temperature, oxygen and sunlight would quickly degrade the "printed" tool into the plastic dust it came from.
The level of engineering and computer skills necessary to 3D model and 3D print a complicated object are comparable to the skills needed to chisel a near likeness of a loved one out of marble. Forget about home economically manufacturing needed items with a home computer for your community with a 3D printer. Even the idea of for publishing a 500 copies of a 16 page newsletter with a home 2D inkjet printer is not economical or realistic.
I agree with Rifkin that "millions of people will create their own energy" but their consumption of energy will be a mere fraction of today's. Home lighting will be doable, but the average home will likely not have enough power for a refrigerator and freezer running 24/7/365.
Moreover, I think the Third Industrial Revolution will take us back to an economy, that existed when I was a child in the mid 20th century, where most things will be made of wood, metal, glass, paper and/or fiber... not a complicated cocktail of petro-chemicals with traces of rare earth elements. Well so much for a critique on techno-optimism and onto Rifkin's article and take on future industrialism.
See also:
Ea O Ka Aina: The Hero's Way 1/13/12 by Juan Wilson
Image above: A plastic rabbit out of a 3D printing tophat called Thing-O-Matic. From (http://www.digitaltrends.com/computing/what-is-3d-printing-a-beginners-guide-to-the-desktop-factory/).
This piece below by Jeremy Rifkin struck me as an exercise in delusional thinking used for mass deception. When Rifkin mentions that "mobile phones, auto and aircraft parts, medical implants, and batteries are being 'printed out' with 3D printers he is talking about industrial design components created by professionals as prototypes - not finished manufactured items.
With the introduction of 3D Systems' first commercial 3D printers, about 20 years ago, the industrial design of mass produced products has been revolutionized - especially complex 3D entities like auto taillight assemblies. But once the design is settled the actual production is still done using plastic injection molding technology.
The idea that your average Joe will design and "print-out" something even as simple as a usable/durable ratchet-set or Vise-grip made out of plastic from a consumer 3D printer hooked up to a laptop is ridiculous. The stresses on these "printed" plastic products would be too great for practical application, moreover temperature, oxygen and sunlight would quickly degrade the "printed" tool into the plastic dust it came from.
The level of engineering and computer skills necessary to 3D model and 3D print a complicated object are comparable to the skills needed to chisel a near likeness of a loved one out of marble. Forget about home economically manufacturing needed items with a home computer for your community with a 3D printer. Even the idea of for publishing a 500 copies of a 16 page newsletter with a home 2D inkjet printer is not economical or realistic.
I agree with Rifkin that "millions of people will create their own energy" but their consumption of energy will be a mere fraction of today's. Home lighting will be doable, but the average home will likely not have enough power for a refrigerator and freezer running 24/7/365.
Moreover, I think the Third Industrial Revolution will take us back to an economy, that existed when I was a child in the mid 20th century, where most things will be made of wood, metal, glass, paper and/or fiber... not a complicated cocktail of petro-chemicals with traces of rare earth elements. Well so much for a critique on techno-optimism and onto Rifkin's article and take on future industrialism.
See also:
Ea O Ka Aina: The Hero's Way 1/13/12 by Juan Wilson
The Third Industrial Revolution
By Jeremy Rifkin on 28 March 2012 for Huffington Post - (http://www.huffingtonpost.com/jeremy-rifkin/the-third-industrial-revo_1_b_1386430.html)
The great economic revolutions in history occur when new communication technologies converge with new energy systems. New energy revolutions make possible more expansive and integrated trade. Accompanying communication revolutions manage the new complex commercial activities made possible by the new energy flows.
Today, Internet technology and renewable energies are beginning to merge to create a new infrastructure for a Third Industrial Revolution (TIR) that will change the way power is distributed in the 21st century. In the coming era, hundreds of millions of people will produce their own renewable energy in their homes, offices, and factories and share green electricity with each other in an "Energy Internet" just like we now generate and share information online. The creation of a renewable energy regime, loaded by buildings, partially stored in the form of hydrogen, distributed via a green electricity Internet, and connected to plug-in, zero-emission transport, opens the door to a Third Industrial Revolution.
While the TIR economy allows millions of people to produce their own virtual information and energy, a new digital manufacturing revolution now opens up the possibility of following suit in the production of durable goods. In the new era, everyone can potentially be their own manufacturer as well as their own internet site and power company. The process is called 3-D printing; and although it sounds like science fiction, it is already coming online, and promises to change the entire way we think of industrial production.
Think about pushing the print button on your computer and sending a digital file to an inkjet printer, except, with 3-D printing, the machine runs off a three-dimensional product. Using computer aided design, software directs the 3-D printer to build successive layers of the product using powder, molten plastic, or metals to create the material scaffolding. The 3-D printer can produce multiple copies just like a photocopy machine. All sorts of goods, from jewelry to mobile phones, auto and aircraft parts, medical implants, and batteries are being "printed out" in what is being termed "additive manufacturing," distinguishing it from the "subtractive manufacturing," which involves cutting down and pairing off materials and then attaching them together.
3-D entrepreneurs are particularly bullish about additive manufacturing, because the process requires as little as 10 percent of the raw material expended in traditional manufacturing and uses less energy than conventional factory production, thus greatly reducing the cost.
In the same way that the Internet radically reduced entry costs in generating and disseminating information, giving rise to new businesses like Google and Facebook, additive manufacturing has the potential to greatly reduce the cost of producing hard goods, making entry costs sufficiently lower to encourage hundreds of thousands of mini manufacturers -- small and medium size enterprises (SMEs) -- to challenge and potentially outcompete the giant manufacturing companies that were at the center of the First and Second Industrial Revolution economies.
Already, a spate of new start-up companies are entering the 3-D printing market with names like Within Technologies, Digital Forming, Shape Ways, Rapid Quality Manufacturing, Stratasys, Bespoke Innovations, 3D Systems, MakerBot Industries, Freedom of Creation, LGM, and Contour Crafting and are determined to reinvent the very idea of manufacturing in the Third Industrial era.
The energy saved at every step of the digital manufacturing process, from reduction in materials used, to less energy expended in making the product, if applied across the global economy, adds up to a qualitative increase in energy efficiency beyond anything imaginable in the First and Second Industrial Revolutions. When the energy used to power the production process is renewable and also generated on site, the full impact of a lateral Third Industrial Revolution becomes strikingly apparent. Since approximately 84 percent of the productivity gains in the manufacturing and service industries are attributable to increases in thermodynamic efficiencies -- only 14 percent of productivity gains are the result of capital invested per worker -- we begin to grasp the significance of the enormous surge in productivity that will accompany the Third Industrial Revolution and what it will mean for society.
The democratization of manufacturing is being accompanied by the tumbling costs of marketing. The internet has transformed marketing from a significant expense to a negligible cost, allowing startups and small and medium size enterprises to market their goods and services on internet sites, like Etsy, that stretch over virtual space, enabling them to compete and even out compete many of the giant business enterprises of the 21st Century.
As the new 3-D technology becomes more widespread, on site, just in time customized manufacturing of products will also reduce logistics costs with the possibility of huge energy savings. The cost of transporting products will plummet in the coming decades because an increasing array of goods will be produced locally in thousands of micro-manufacturing plants and transported regionally by trucks powered by green electricity and hydrogen generated on site.
The lateral scaling of the Third Industrial Revolution allows small and medium size enterprises to flourish. Still, global companies will not disappear. Rather, they will increasingly metamorphose from primary producers and distributors to aggregators. In the new economic era, their role will be to coordinate and manage the multiple networks that move commerce and trade across the value chain.
The rapid decline in transaction costs brought on by The Third Industrial Revolution are leading to the democratization of information, energy, manufacturing, marketing, and logistics, and the ushering in of a new era of distributed capitalism that is likely to change the very way we think of commercial life in the 21st Century.
.